Back in early April, I mentioned a facial recognition program called RecognizeMe, available for "jailbroken" Apple iOS-based hardware. I went ahead and dropped $2.99 on the program, then installed it on my fourth-generation iPod touch and two iPhone 4s (AT&T and Verizon); my first-generation iPad doesn't have a front-facing camera and is therefore not a testing candidate.
I've spent about an hour with the application on both above hardware platforms, since the iPod touch contains a prior-generation ARM CPU/GPU combination and also has clock speed and system memory allocation deficits versus the iPhone 4. This may not be a tremendous amount of training attention, perhaps, but on the other hand i suspet it's more time than most users will bother devoting. And so far I'm not very impressed.
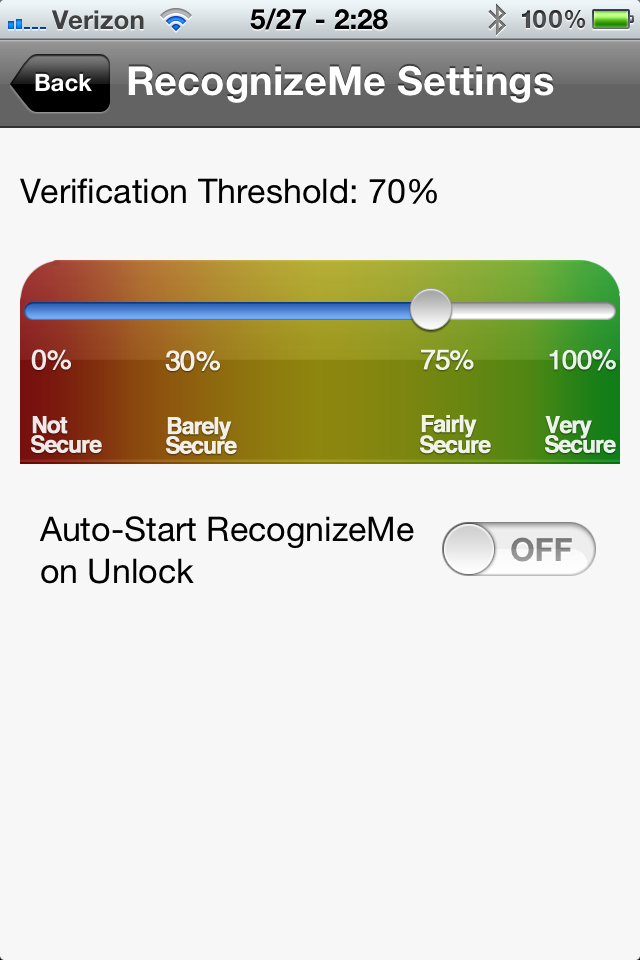
Although RecognizeMe v2 claims to notably improve recognition speed versus v1 (which I haven't used), in part by leveraging hardware acceleration via iOS 5's CoreImage API, the facial recognition algorithm still takes a lengthy amount of time to validate my identity and unlock the device…assuming it makes a match at all. And in order to get a reasonable success rate, I need to lower the verification threshold far below the level that the developer's own documentation suggests is necessary for "best security."
The visual effects, at least, are pretty neat. When you start the program, it shows you by means of a ghostly green 'mask' (complete with eyeball cutouts) where it's discerned your facial outlines are, along with an up-and-down sweeping red line to indicate the data-collection vertical boundaries:

Press 'Train', and the program begins collecting 14 sequential images:

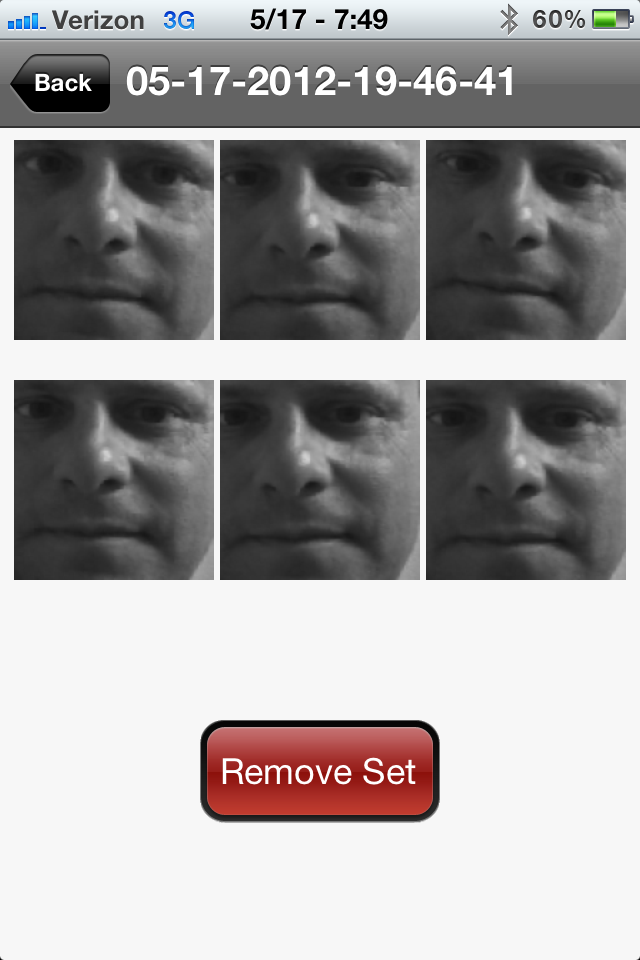
which it then converts into a biometric training set:

that looks something like this:
Next, you enable the passcode lock feature in the iOS device settings. From that point on, every time you swipe the device unlock screen, RecognizeMe will automatically first launch and attempt to identify you. If it times out and gives up, you're then presented with the numeric keypad interface as an alternative unlock scheme…one that I found myself using far too frequently.
The developer's literature claims that RecognizeMe will continue to work even if you capture the initial biometrics without glasses on your face but later put them on, or visa versa, but this aspiration didn't match my experiences. More generally, it recommends that you create at least 4-5 biometric training sets, across a range of lighting conditions. However, it also includes several important qualifier statements (which I've grammatically corrected in the quotes below):
Maintain at least a 65% verification threshold for best security.
There are tradeoffs. More biometric training sets mean better accuracy, but a slower verification time.
and
Again, there's a tradeoff. A higher threshold means it's more likely that the algorithm won't recognize you, and recognition will also take longer. A lower threshold means faster results, but also more of a chance of false positives slipping through.
In my experience so far, even if I don't change lighting conditions (or for that matter, even my location or position) between training set creation and subsequent attempted identity verification, RecognizeMe doesn't successfully…err…recognize me unless I drop the verification threshold well below 50%. In such a situation, I wouldn't feel confident that RecognizeMe would have a sufficiently low "false positive" rate to ensure adequate security. And even with an abnormally low verification threshold, assessing a match still takes a painfully long amount of time, much slower than just punching a code into the on-screen numeric keypad.
I'll keep periodically experimenting with RecognizeMe, and if I achieve any notable breakthroughs (either via my training and configuration methodology or the developer's program upgrades), I'll report back. I also have no idea how RecognizeMe's performance and accuracy compare against that of the facial recognition algorithms built into Google's Android 4. But based on my experiences so far, although the facial unlock feature is mildly entertaining, it's not yet practical. Then again, though, I could say the same thing about the "beta" Siri voice recognition built into Apple's iPhone 4s…